SOC 2 is an external audit report provided by a CPA firm on the design (Type 1) and operating effectiveness (Type 2) of the implemented controls.
SOC 2 has 5 trust criterias based on the AICPA Trust Principles (TSP) that assesses the implemented controls against the COSO standards.
- Security – Are information assets and critical systems protected against unauthorized access, unauthorized disclosure of information, and damage to systems that could compromise the availability, integrity, confidentiality, and privacy of information or systems and affect the entity’s ability to meet its objectives?
- Availability – Are information assets and critical systems available for operation and use to meet the entity’s objectives?
- Processing Integrity – Is system processing complete, valid, accurate, timely, and authorized to meet the entity’s objectives?
- Confidentiality – Is information designated as confidential is protected to meet the entity’s objectives?
- Privacy – Is personal information collected, used, retained, disclosed, disposed and secured to meet the entity’s objectives?
Like many audit standards such as COBIT, the AICPA, SOC 2 TSPs are also based on COSO principles of auditing. Of these principles, the Common Criteria 4.1 (CC4.1) states that:
COSO Principle 16: The entity selects, develops, and performs ongoing and/or separate evaluations to ascertain whether the components of internal control are present and functioning.
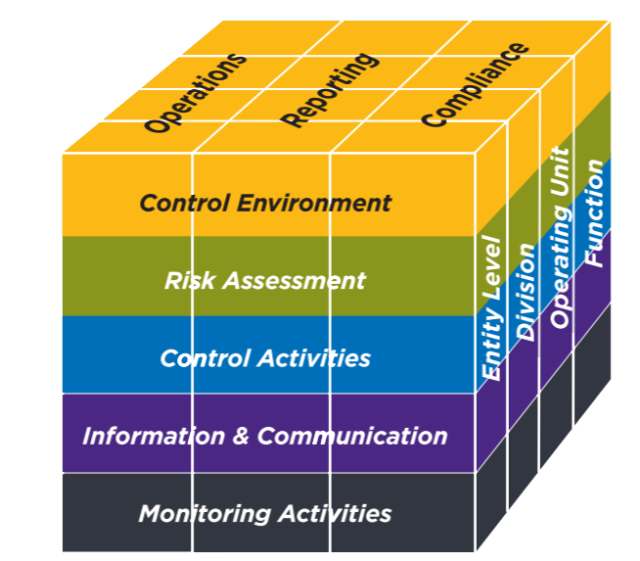
The Point of Focus for this Principle reads as “Considers Different Types of Ongoing and Separate Evaluations—Management uses a variety of different types of ongoing and separate evaluations, including penetration testing, independent certification made against established specifications (for example, ISO certifications), and internal audit assessments.” and often the Illustrative Control Activity from the auditor requires an annual penetration test to be performed an annual basis.
Similarly, the CC7.1 reads as – “To meet its objectives, the entity uses detection and monitoring procedures to identify (1) changes to configurations that result in the introduction of new vulnerabilities, and (2) susceptibilities to newly discovered vulnerabilities.” with a point of focus – “The entity conducts vulnerability scans designed to identify potential vulnerabilities or misconfigurations on a periodic basis and after any significant change in the environment and takes action to remediate identified deficiencies on a timely basis.”, and the illustrative activity either requesting for a vulnerability assessment or a penetration test performed within the audit period.
How ABIR Networks can help you achieve SOC 2 compliance?

With a team of expert Penetration Testers and SOC 2 advisors, ABIR Networks helps you right from scoping the environment for the test to the perform the actual test. Our approach for SOC 2 compliant penetration test includes not only automated tools and scanning but testing for findings and vulnerabilities manually using the guiding principles from OWASP Top 10 and SANS 25 reports, including the Gray box testing for business logic and validation checks. Our SOC 2 advisors have advised 20+ organizations perform the end-to-end assessment and our expert team of Pentesters bring 60+ years of cumulative experience with industry recognized certifications such as OSCP, CEH, CREST, CISSP, & CISA to name a few. Get in touch with us today for a free consultation call.
References:
2017 Trust Services Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy – link